I’ve been deploying Exchange in a hosted environment for well over 10 years now – starting with ADSI hacks in Exchange 2000 and 2003, then using DotNetPanel (now called WebSitePanel) in Exchange 2007, which worked amazingly well and from the administration standpoint is a GREAT product.
Now with Exchange 2010, in service pack 1 they’ve added 2 very important switches: /hosting for the install portion, and /organization for setup of individual hosted organizations. The following is how I’ve deployed Exchange 2010 in this mode so it’s ready for use.
References:
http://www.yusufozturk.info/exchange-server/hosted-exchange-2010-setup-guide-part-1.html
First, let’s stage up 2 VMS – a HT/CAS server and an MBX server. These will run Windows 2008 R2 and be joined to your AD domain
Make sure the server has Windows 2008 R2 SP1 – this skips the need for the 5 prerequiste hotfixes:
http://technet.microsoft.com/en-us/library/bb691354.aspx
If you don’t have SP1 installed, you can grab a ZIP file from my Skydrive with all of the prerequisite file and save yourself some time on the download: E2010SP1-prereq.zip
Download and install the Office 2010 Filter Pack:
http://www.microsoft.com/download/en/details.aspx?id=17062
Run the special prereqscript.ps1 script from my LiveDrive to install the necessary server roles/features needed, reboot when necessary.
Extend AD for the roles
d:\setup.com /PrepareAD /OrganizationName:Sandbox
Setup the MBX role on the first server
d:\setup.com /mode:install /role:”MB,MT” /organizationName:”Sandbox” /hosting
Setup the HT and CAS role
d:\setup.com /mode:install /role:”CA,HT,MT” /organizationName:”Sandbox” /hosting
On the HT server, let’s setup some mail connectors:
First, the receive connector from the internet
New-ReceiveConnector -Name ‘Inbound SMTP Array’ -Usage ‘Custom’ -Bindings ‘10.20.110.11:25’ -Fqdn ‘mail.memphistech.net’ -RemoteIPRanges ‘0.0.0.0-255.255.255.255’ -Server ‘SBXCAS1’ -PermissionGroups:AnonymousUsers,ExchangeUsers,ExchangeServers
Second, the second connector TO the internet
New-SendConnector -Name ‘Outbound SMTP Gateway’ -Usage ‘Custom’ -AddressSpaces ‘SMTP:*;1’ -DNSRoutingEnabled $true -UseExternalDNSServersEnabled $false -Fqdn ‘mail.memphistech.net’ -SourceTransportServers ‘SBXCAS1’
Now, let’s create our certificate request
New-ExchangeCertificate -FriendlyName ‘mail.memphistech.net’ -GenerateRequest -PrivateKeyExportable $true -KeySize ‘2048’ -SubjectName ‘C=US,S=”Minneapolis”,L=”Minnesota”,O=”Memphistech”,OU=”IT”,CN=mail.memphistech.net’ -DomainName ‘mail.memphistech.net’,’autodiscover.memphistech.net’,’SBXCAS1.sandbox.local’,’SBXCAS2.sandbox.local’,’SBXMBX1.sandbox.local’,’SBXMBX2.sandbox.local’ -Server ‘SBXCAS1’
Note: while some people prefer to only use the NETBIOS names of the servers, Windows works in a DNS/FQDN-based world so we are using the full server name.
In Exchange 2010 you have to copy and paste the CSR request from the Powershell window
—–BEGIN NEW CERTIFICATE REQUEST—–
MIIEoDCCA4gCAQAweTEdMBsGA1UEAwwUbWFpbC5tZW1waGlzdGVjaC5uZXQxCzAJ
BgNVBAsMAklUMRQwEgYDVQQKDAtNZW1waGlzdGVjaDESMBAGA1UEBwwJTWlubmVz
b3RhMRQwEgYDVQQIDAtNaW5uZWFwb2xpczELMAkGA1UEBhMCVVMwggEiMA0GCSqG
SIb3DQEBAQUAA4IBDwAwggEKAoIBAQCdKuUAwRpFPW/12mjfbdrbykLznT+tquri
DUdOeCVayYiYlul5cSwg0yOITct9jaTCk3OaJJwxkGcJ7fI/gLfEztTJLLlGn66a
71J5Am9JJ+g9ScsTzbA+Y1yoB23HZ7Zw2OZO/Ib4IAsZ89NURaXfxx5DDHxvxSf4
G48jQBFJDoulVQBEBTdKlF6JMoBodIKoNTbHovYwuDvJAk5uOZuZLmW1kTEyk0Ym
AAjpXKP3i4YilTuC4F/mI6pMIghetEI6rHKaf8x+/AEWtcNnNYr64LBXFaxpJoyS
INrb+OQu/5JAIbUfF0G1RxgVAzlxpH8vJ75owKHu7PUCc/OLeN25AgMBAAGgggHg
MBoGCisGAQQBgjcNAgMxDBYKNi4xLjc2MDAuMjBfBgkrBgEEAYI3FRQxUjBQAgEF
DBVTQlhDQVMxLnNhbmRib3gubG9jYWwMEFNBTkRCT1hcU0JYQ0FTMSQMIk1pY3Jv
c29mdC5FeGNoYW5nZS5TZXJ2aWNlSG9zdC5leGUwcgYKKwYBBAGCNw0CAjFkMGIC
AQEeWgBNAGkAYwByAG8AcwBvAGYAdAAgAFIAUwBBACAAUwBDAGgAYQBuAG4AZQBs
ACAAQwByAHkAcAB0AG8AZwByAGEAcABoAGkAYwAgAFAAcgBvAHYAaQBkAGUAcgMB
ADCB7AYJKoZIhvcNAQkOMYHeMIHbMA4GA1UdDwEB/wQEAwIFoDCBmwYDVR0RBIGT
MIGQghRtYWlsLm1lbXBoaXN0ZWNoLm5ldIIcYXV0b2Rpc2NvdmVyLm1lbXBoaXN0
ZWNoLm5ldIIVU0JYQ0FTMS5zYW5kYm94LmxvY2FsghVTQlhDQVMyLnNhbmRib3gu
bG9jYWyCFVNCWE1CWDEuc2FuZGJveC5sb2NhbIIVU0JYTUJYMi5zYW5kYm94Lmxv
Y2FsMAwGA1UdEwEB/wQCMAAwHQYDVR0OBBYEFKTLbPuDO1HY+lTb26Jb4M/Lrs5v
MA0GCSqGSIb3DQEBBQUAA4IBAQA5Um0c5S4rcG/+eIdOvl/aSa6CDMfOFyUIxTgM
IPJMpFYC/a/1KIP3wwFIHsiI9V4s9AOf0IgbV4bvTQEHRo62L5F7EzSw27xecLrr
253HJ9ClyRn/AIqVH1E1KebgT5Z9omQrCud4DJ6p6Ju+Pu8V3cjPKskKzbhahQPL
phouxTRXRqOMpZ2+WDiJZcLMUpB0P+5crkuv+t1Tx4x5iAjqb2S26I/Z1ZEjvK5A
fHiann5QWfiqOwB6mxnDbuAhZRIEAPN4tjEHwC6WQ/bSJstKQkaHUx60t2J8S3GU
XGc3sHW2k5okhlSn3H6thz6ZpFJ+0YFxDQOluDoDd6WQl1vC
—–END NEW CERTIFICATE REQUEST—–
So instead, issue the Set-Content command to output it to file
http://www.proexchange.be/blogs/exchange2010/archive/2009/10/23/generating-exchange-2010-certificates-exchange-management-shell.aspx
Set-Content -path “c:\e2010.req” -Value (New-ExchangeCertificate -FriendlyName ‘mail.memphistech.net’ -GenerateRequest -PrivateKeyExportable $true -KeySize ‘2048’ -SubjectName ‘C=US,S=”Minneapolis”,L=”Minnesota”,O=”Memphistech”,OU=”IT”,CN=mail.memphistech.net’ -DomainName ‘mail.memphistech.net’,’autodiscover.memphistech.net’,’SBXCAS1.sandbox.local’,’SBXCAS2.sandbox.local’,’SBXMBX1.sandbox.local’,’SBXMBX2.sandbox.local’ -Server ‘SBXCAS1’)
Now let’s submit the certificate to our local CA, but first on our CA we need to make sure that its setup:
http://exchangeserverpro.com/how-to-issue-a-san-certificate-to-exchange-server-2010-from-a-private-certificate-authority
From a command prompt, type certutil -getreg policy\EditFlag
If there is no EDITF_ATTRIBUTESUBJECTALTNAME2 flag then you can enable it by running the following command.
certutil -setreg policy\EditFlags +EDITF_ATTRIBUTESUBJECTALTNAME2
Now restart the certificate authority
net stop certsvc && net start certsvc
Now go through the process of accessing the web enrollment page to paste in the CSR and then download the finalized certificate
Once you have the file downloaded, import the certificate
Import-ExchangeCertificate -FileData ([Byte[]]$(Get-Content -Path C:\mail.memphistech.net.cer -Encoding byte -ReadCount 0)) -Password:(Get-Credential).password
Perform a Get-ExchangeCertificate and match up the “FriendlyName” we gave earlier to the correct thumbprint, and copy it to the clipboard
Then, assign it to the necessary services (IMAP | POP | UM | IIS | SMTP)
http://technet.microsoft.com/en-us/library/aa997231.aspx
Enable-ExchangeCertificate -Server ‘SBXCAS1’ -Services IMAP,POP,IIS,SMTP -Thumbprint 86D7D2FD0E50AFD3CE74A125C4BAF6DD65659006
Now let’s export the certificate for use with our other servers:
$File = Export-ExchangeCertificate -Thumbprint 86D7D2FD0E50AFD3CE74A125C4BAF6DD65659006 -BinaryEncoded:$true -Password (Get-Credential).password
Set-Content -Path “C:\e2010all.pfx” -Value $File.FileData -Encoding Byte
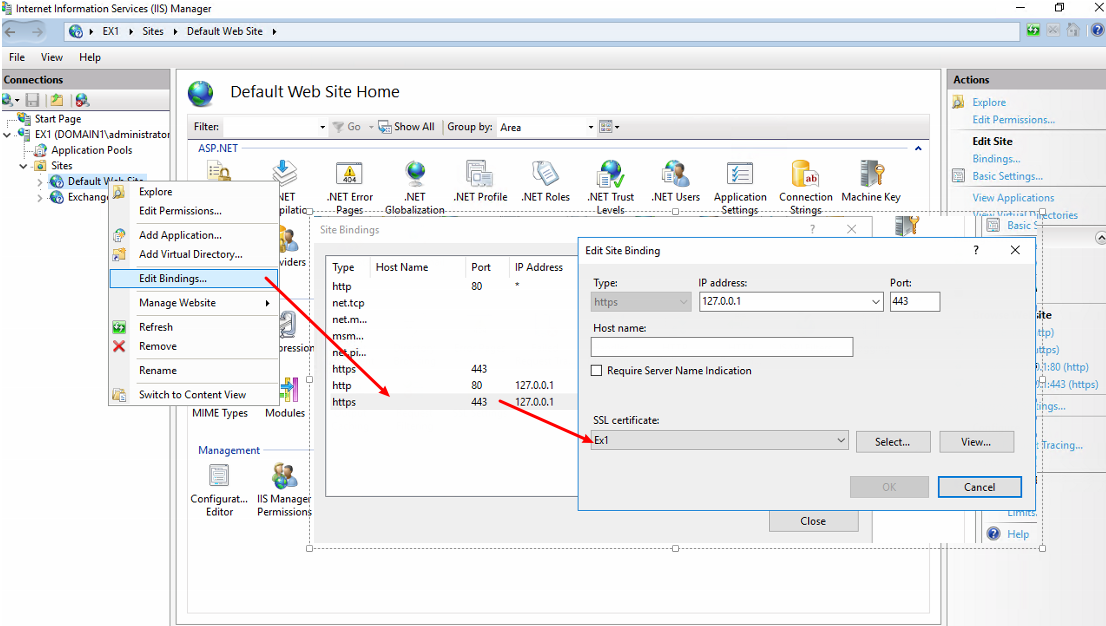
Once you have the certificates installed, you are ready to test external access!
To make redirection to the OWA URL easier, grab the e2010redir.zip file from my SkyDrive, copying the 403.htm and 403-4.htm to the c:\inetpub\custerr\en-US, and default.htm
to c:\inetpub\wwwroot. Remove iisstart.htm from c:\inetpub\wwwroot.
Next, open 80/443 to your CAS server in your firewall.
Finally, add DNS records pointing to your public IP. I then type mail.memphistech.net in my browser and its automatically redirected to the login page.