I always have a rule of thumb “if it takes more than an hour to solve, it deserves sharing”, and that’s always been the story of my blogs over the last decade plus. The biggest struggle is finding the time to sit down, pull all my notes together, and sharing it with the larger IT community. With the Thanksgiving 2019 holiday weekend and time off (and I’m not WORKING working), time to dig into the Microsoft Modern Workplace space I spend most of my time architecting, deploying & speaking about!
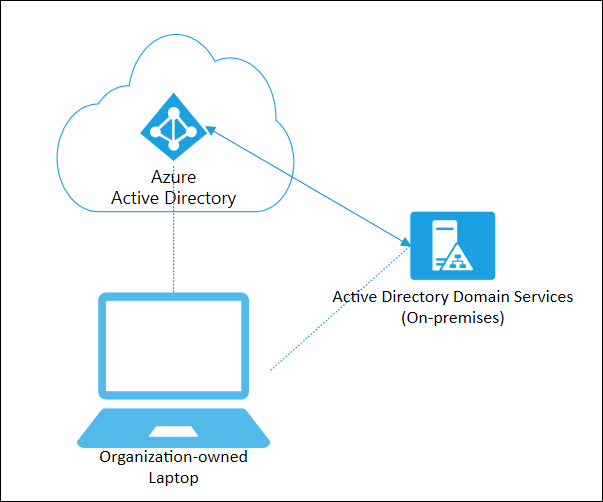
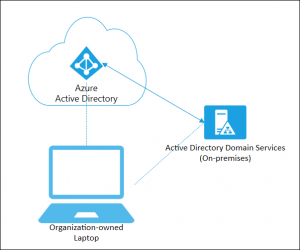
This edition will cover a topic that has been near and dear (and a pain in my rear) to me, and it has to do with the Microsoft Device Management story as it pertains to Hybrid AD devices. Azure AD is the nirvana, mountain top goal that all organizations should be aiming, but as a realist in recognizing that takes time, time, and more time, starting off with Cloud management is a baby step in bringing the rest of an organization.
To meet the prerequisites for the SCCM Co-Management story, Hybrid AD and Intune registered devices for MDM are necessary; see:
https://docs.microsoft.com/en-us/configmgr/comanage/overview#prerequisites
In a Hybrid AD scenario this requires line of sight to a domain controller (which also applies to AutoPilot and Hybrid AD, but that’s for another Volume), but what happens with a remote workforce? Let’s dig into the “gotchas” to bring these devices into the fold.
Contents
Hybrid AD PC Connectivity
The first step of populating your PCs into Azure AD is to ensure AD Connect has “Device Writeback” properly configured; see:
https://docs.microsoft.com/en-us/azure/active-directory/hybrid/how-to-connect-device-writeback
Also – be sure your users have an Azure Active Directory Premium (P1/P2) license assigned!!
Once this is configured, and PCs begin to sync into Azure AD, you’re halfway there – but only the easiest part is done! The next step is changing that Pending status under Registered to showing a last contacted timestamp. For your remote workforce, this requires some Jedi-like
Connect the machine to your network!
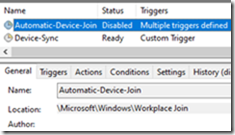
In the field, there are still a number of PC clients that do not support connection at the login screen. This is typically where the Workplace Join task typically fires off at log in, but because there is no network connectivity / line-of-site to the domain controller, we need to manually kick off the Hybrid AD Join process.
Fire up Task Scheduler and down under the Microsoft\Windows folder, run the Automatic Device Join task
Once it’s had a chance to run, NOW REBOOT!
After a few moments you should see the status of the Device in Azure AD with a Timestamp
Registering with Intune
This one is a little trickier because there are some GOTCHAs to make this work properly:
- Windows 10 at 1709 or higher
- GPO to push the MDM registration!
https://docs.microsoft.com/en-us/windows/client-management/mdm/enroll-a-windows-10-device-automatically-using-group-policy
Also – be sure your users have an Intune license assigned!!
After you’ve performed the Hybrid AD join, login as the user and fire up a command prompt to run Dsregcmd /status to validate MDM URLS are populated. This should happen after the Azure AD join.

Once you see these, LOG OFF and back on.
If you still are running into a wall, maybe it’s time to check out my more recently blog
Effortlessly Conquor Common Microsoft MDM Enrollment Errors
The Ghost of SCCM
In some cases where Configuration Manager agent was uninstalled but the PC is still reporting as Externally Managed. In this case change the following registry key
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Enrollments
ExternallyManaged REG_DWORD to 0
Wait 30-60 seconds
Check under the Device Management event viewer for status, which is at:
Microsoft-Windows-DeviceManagement-Enterprise-Diagnostics-Provider/Admin
This process can take a little bit of time to allow the back and forth communication between the machine and the Intune service.
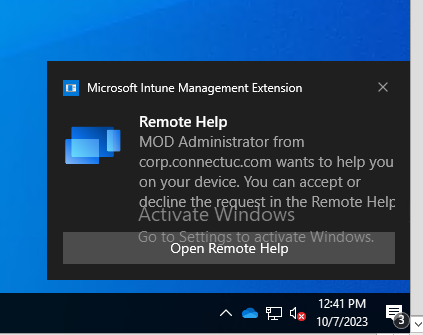
If everything is successful, the first thing you should see Intune Management Extension installation (which you can validate under the Service MMC) and Company portal install
Finally, once all is well inside of Azure AD you should see MDM as Microsoft Intune
Once these are complete, any Device Configuration and Compliance policies you have set
In Closing
In the ever-evolving field of Cloud Device Management, these Notes From The Field should help in troubleshooting the first step of a Co-Managed environment, no matter where in the world your Hybrid AD devices may be housed.