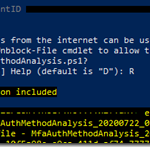
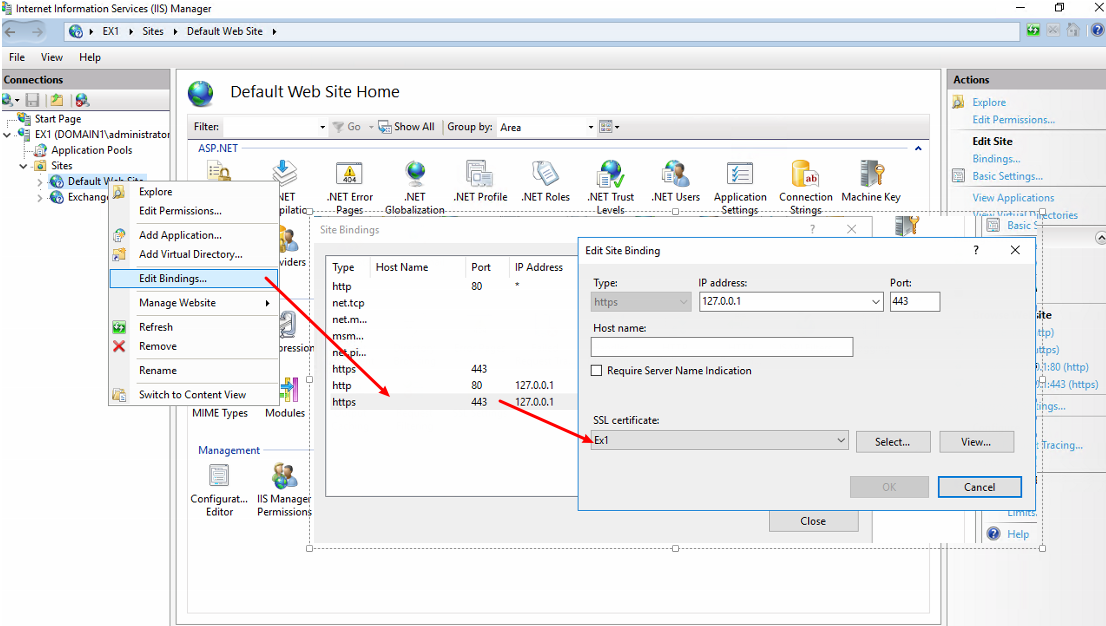
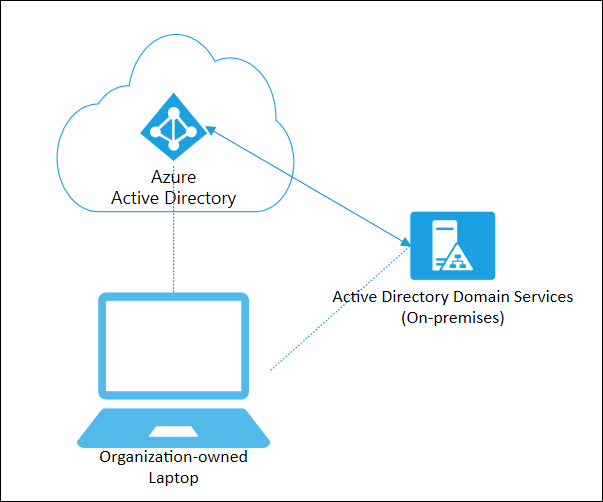
Microsoft recently released a very helpful script that allows Administrators looking to roll out Azure MFA to their organization with a easy-to-read output that can aid in assessing status, or even recommendations to enhance...
Read More
2 Minutes